Where do hackers learn?
In this regard, what kind of jobs do hackers get?
After attaining the much coveted CEH v10, an ethical hacker can try for the following roles:
- Information Security Analyst.
- Security Analyst.
- Certified Ethical Hacker (CEH)
- Ethical Hacker.
- Security Consultant, (Computing / Networking / Information Technology)
- Information Security Manager.
- Penetration Tester.
Furthermore, where do hackers get their information? Hackers can figure out your passwords by stalking your social media profiles to find information commonly used in passwords such as children's names, or they can simply try out a list of commonly used passwords until they hit the right one.
Correspondingly, what language do hackers use?
Programming languages that are useful to hackers
| SR NO. | COMPUTER LANGUAGES | DESCRIPTION |
|---|---|---|
| 1 | HTML | Language used to write web pages. |
| 2 | JavaScript | Client side scripting language |
| 3 | PHP | Server side scripting language |
| 4 | SQL | Language used to communicate with database |
What do hackers study in college?
It is important to have a Bachelor's degree (BSc, BTech, BE, BCA) in Information Technology or Computer Science to become an ethical hacker. Candidates with advanced diploma in network security or relevant technology can also choose ethical hacking as professional career.
Related Question Answers
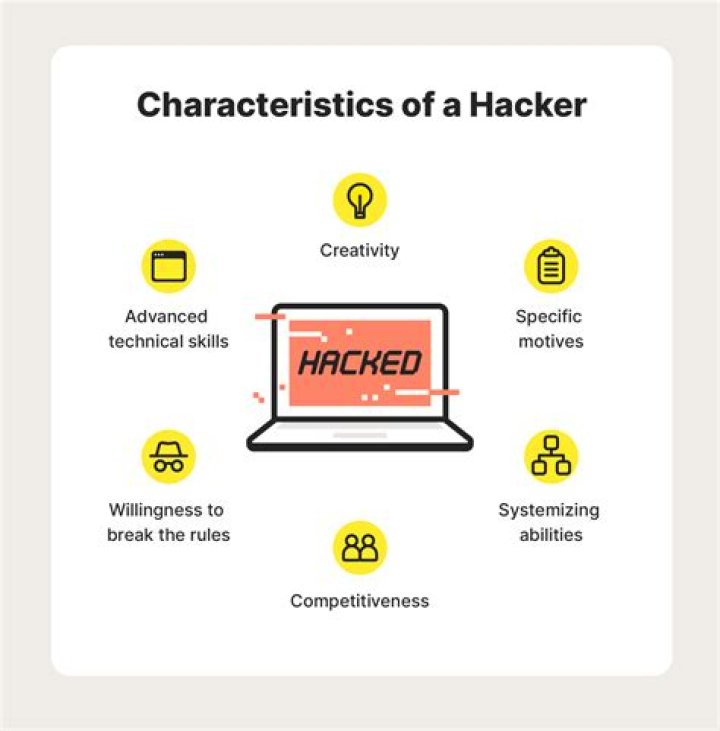
Are hackers in demand?
The job outlook for IT security is expected to grow by 32% from 2018 to 2028. The reason behind this rise is the growing frequency of cyber threats and security incidents. To deal with these incidents, we need a strong line of defense, that includes Ethical Hackers.How do hackers earn?
Theoretically, it's the simplest way to monetise a hack. Through sophisticated phishing tactics or simply by dropping malware once access has been gained to a network, hackers can begin encrypting crucial files and charge a hefty sum (usually in Bitcoin) to unencrypt them.Can I become an ethical hacker?
At this point in your career, you should be aiming at getting a Certified Ethical Hacker (CEH) certification from the International Council of Electronic Commerce Consultants (the EC Council). The training you receive will take you through everything you need to know to become an efficient, ethical hacker.Can a commerce student become a hacker?
Candidates who are applying for the degree and diploma courses in hacking must be residents of India. The applicants must not be less than 21 years of age when they apply for the course. There are well known institutes in India offering courses in Ethical Hacking.How can I get job in Google?
Apply for a job- Once you've found a job you want to apply for, click the APPLY button near the top of the job description.
- Sign in to your Google Account. Take note of which email you use to sign in and apply. We'll send you notifications and updates at this address.
- Upload your resume, fill out the form, review, and submit it.
How much are ethical hackers paid?
In India on an average a certified ethical hacker earns an average salary of Rs 3,67,249 per year which increases with experience cumulatively upto more than 15 lakh per year. According to Payscale.com the current average salary of a CEH professional is $ 90,000 or INR 64,06,560 per year.What are the requirements to become a hacker?
There are no standard education criteria for a white hat hacker – every organization can impose its own requirements on that position – but a bachelor's or master's degree in information security, computer science or even mathematics provides a strong foundation.Is being a hacker a job?
One of the most in-demand positions in this field is that of an ethical hacker—an IT professional who purposefully penetrates networks and systems to find and fix potential vulnerabilities. If you're looking to put on your “white hat” and infiltrate systems for good, this position can be a great career opportunity.Can I hack using a phone?
With just a few taps, an Android phone can be weaponized into a covert hacking device capable of running tools such as Nmap, Nikto, and Netcat — all without rooting the device. With this, it's possible to run an ARM64 Debian operating system alongside the current Android OS.Can you use Python to hack?
Python is a widely used general-purpose, high-level programming language. Python is a very simple language yet powerful scripting language, it's open-source and object-oriented and it has great libraries that can be used for both for hacking and for writing very useful normal programs other than hacking programs.How do you hack hackers?
Here are a few key terms that you'll hear in discussions about hackers and what they do:- Back door. A secret pathway a hacker uses to gain entry to a computer system.
- Buffer overflow.
- Denial-of-service attack.
- Email worm.
- Root access.
- Root kit.
- Script kiddie.
- Session hijacking.
How long does it take to become a hacker?
Most people who try can obtain a decent skill set in eighteen months to two years if they completely concentrate on it. However, hacking is a vast ocean which takes years to explore its mystery.Do hackers use C++?
There are typically five main languages that are most helpful for hackers to know. C and C++ are probably the most powerful low level languages at the disposal of programers today. C and C++ give the user access to low level resources such as ram and system processes.Who is the best hacker in the world?
Top 10 Most Notorious Hackers of All Time- Kevin Mitnick. A seminal figure in American hacking, Kevin Mitnick got his start as a teen.
- Anonymous. Anonymous got its start in 2003 on 4chan message boards in an unnamed forum.
- Adrian Lamo.
- Albert Gonzalez.
- Matthew Bevan and Richard Pryce.
- Jeanson James Ancheta.
- Michael Calce.
- Kevin Poulsen.