What is the formula to encrypt in RSA algorithm?
Also know, what is the encryption formula?
The conversion formula is of the form c ≡ p + a mod 26. So a ≡ 5 37 Page 4 mod 26, and the encryption formula is c ≡ p + 5 mod 26. The ciphertext is thus obtained by shifting 5 to the right, and so deciphering shifts 5 to the left: p ≡ c − 5 mod 26. Now work letter by letter.
Subsequently, question is, how do I encrypt text with RSA? Enter 1st prime number p 13 Enter 2nd prime number q 19 the value of z = 216 the value of e = 5 the value of d = 173 Plain text as sequence of numbers: [83, 101, 99, 114, 101, 116, 46] Encrypted message is: [239.0, 43.0, 112.0, 95.0, 43.0, 51.0, 50.0] Decrypted message is: Secret.
Similarly, you may ask, what is the encryption operation of RSA?
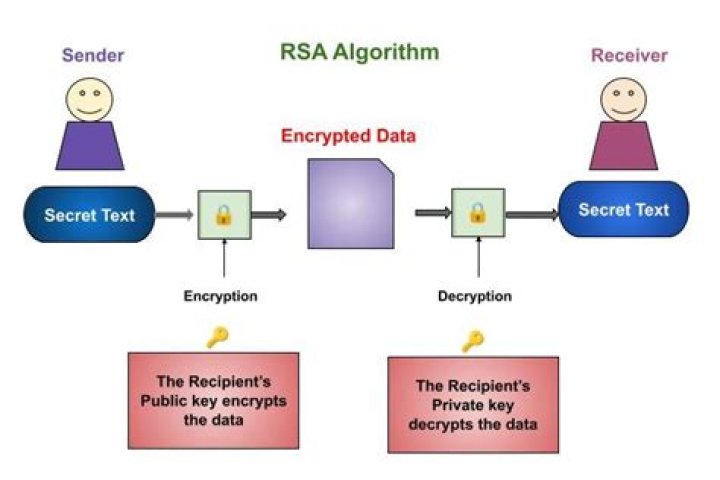
Under RSA encryption, messages are encrypted with a code called a public key, which can be shared openly. Due to some distinct mathematical properties of the RSA algorithm, once a message has been encrypted with the public key, it can only be decrypted by another key, known as the private key.
What is encryption example?
Encryption is a means of securing digital data using one or more mathematical techniques, along with a password or "key" used to decrypt the information. For example, websites that transmit credit card and bank account numbers should always encrypt this information to prevent identity theft and fraud.
Related Question Answers
How do you decode ciphers?
All substitution ciphers can be cracked by using the following tips:- Scan through the cipher, looking for single-letter words.
- Count how many times each symbol appears in the puzzle.
- Pencil in your guesses over the ciphertext.
- Look for apostrophes.
- Look for repeating letter patterns.
How do you crack an affine cipher?
Since we know that each letter in plaintext is enciphered in the function of y = (ax + b) MOD m, we can break the affine cipher by solving two linear equations with two examples of x and y. Once we obtain the values of a and b, we can decipher the entire ciphertext. For example, Assume that “IF†is enciphered as “PQâ€.Can RSA be broken?
Breaking RSA encryption is known as the RSA problem. Whether it is as difficult as the factoring problem is an open question. There are no published methods to defeat the system if a large enough key is used. RSA is a relatively slow algorithm.How secure is RSA?
RSA is secure, but it's being implemented insecurely in many cases by IoT manufacturers. More than 1 in every 172 RSA keys are at risk of compromise due to factoring attacks. ECC is a more secure alternative to RSA because: ECC keys are smaller yet more secure than RSA because they don't rely on RNGs.What comes first encryption or decryption?
Encryption is the process of converting normal message (plaintext) into meaningless message (Ciphertext). Whereas Decryption is the process of converting meaningless message (Ciphertext) into its original form (Plaintext). whereas secret writing is that the recovery of the first message from the encrypted information.What is N in RSA algorithm?
A modulus, n, is calculated by multiplying p and q. This number is used by both the public and private keys and provides the link between them. Its length, usually expressed in bits, is called the key length.What is RSA algorithm and how it works?
RSA algorithm is asymmetric cryptography algorithm. Asymmetric actually means that it works on two different keys i.e. Public Key and Private Key. As the name describes that the Public Key is given to everyone and Private key is kept private.Why do we use RSA key?
RSA is a cryptosystem for public-key encryption and is widely used for securing sensitive data, particularly when being sent over an insecure network such as the Internet.What is the use of RSA algorithm?
RSA (Rivest–Shamir–Adleman) is an algorithm used by modern computers to encrypt and decrypt messages. It is an asymmetric cryptographic algorithm. Asymmetric means that there are two different keys. This is also called public key cryptography, because one of the keys can be given to anyone.Is RSA still used today?
But RSA still has a friend: the TLS standard used in HTTPs, and where it is one of the methods which is used for key exchange and for the signing process. Most of the certificates that are purchased still use RSA keys. And so RSA is still hanging on within digital certificates, and in signing for identity.What is the key size of RSA?
For RSA keys, the minimum size for clear RSA keys and secure RSA keys on the public key data set (PKDS) is 512 bits.Size considerations for public and private keys.
| RSA key size | NISTECC key size | BPECC key size |
|---|---|---|
| 1024 bits | 192 bits | 160 or 192 bits |
| 2048 bits | 224 bits | 224 bits |
| 3072 bits | 256 bits | 256 or 320 bits |
| 7680 bits | 384 bits | 384 bits |
How do you solve RSA algorithm problems?
RSA Algorithm Example- Choose p = 3 and q = 11.
- Compute n = p * q = 3 * 11 = 33.
- Compute φ(n) = (p - 1) * (q - 1) = 2 * 10 = 20.
- Choose e such that 1 < e < φ(n) and e and φ (n) are coprime.
- Compute a value for d such that (d * e) % φ(n) = 1.
- Public key is (e, n) => (7, 33)
- Private key is (d, n) => (3, 33)
Is RSA 1024 secure?
For example, the security available with a 1024-bit key using asymmetric RSA is considered approximately equal in security to an 80-bit key in a symmetric algorithm. The actual degree of security achieved over time varies, as more computational power and more powerful mathematical analytic methods become available.How do you implement RSA?
Key generation- Step 1: find two random, very large prime numbers p and q and calculate. .
- Step 2: select a small odd integer e that is relatively prime to.
- For where p and q are primes, we get.
- Step 3: compute d as the multiplicative inverse of e modulo.
- At this point we have all we need for the public/private keys.
How do I unencrypt private key?
Removing a passphrase using OpenSSL- Copy the private key file into your OpenSSL directory (or specify the path in the command below).
- Run this command: openssl rsa -in [original.key] -out [new.key]
- Enter the passphrase for the original key when asked.
- The output file [new. key] should now be unencrypted.
What is RSA algorithm with example?
RSA algorithm is an asymmetric cryptography algorithm which means, there should be two keys involve while communicating, i.e., public key and private key. There are simple steps to solve problems on the RSA Algorithm. and should not divide by 20.What does an RSA key look like?
A RSA public key consists in two integers, the modulus (n) and the public exponent (e). It is normally encoded as an ASN. 1 structure that is a SEQUENCE of two INTEGER values.What are the possible attacks on RSA?
Possible Attacks on RSA- Searching the Message Space. One of the seeming weaknesses of public key cryptography is that one has to give away to everybody the algorithm that encrypts the data.
- Guessing d.
- Cycle Attack.
- Common Modulus.
- Faulty Encryption.
- Low Exponent.
- Factoring the Public Key.



